Ogarev
A release for the pinpad named ogarev.
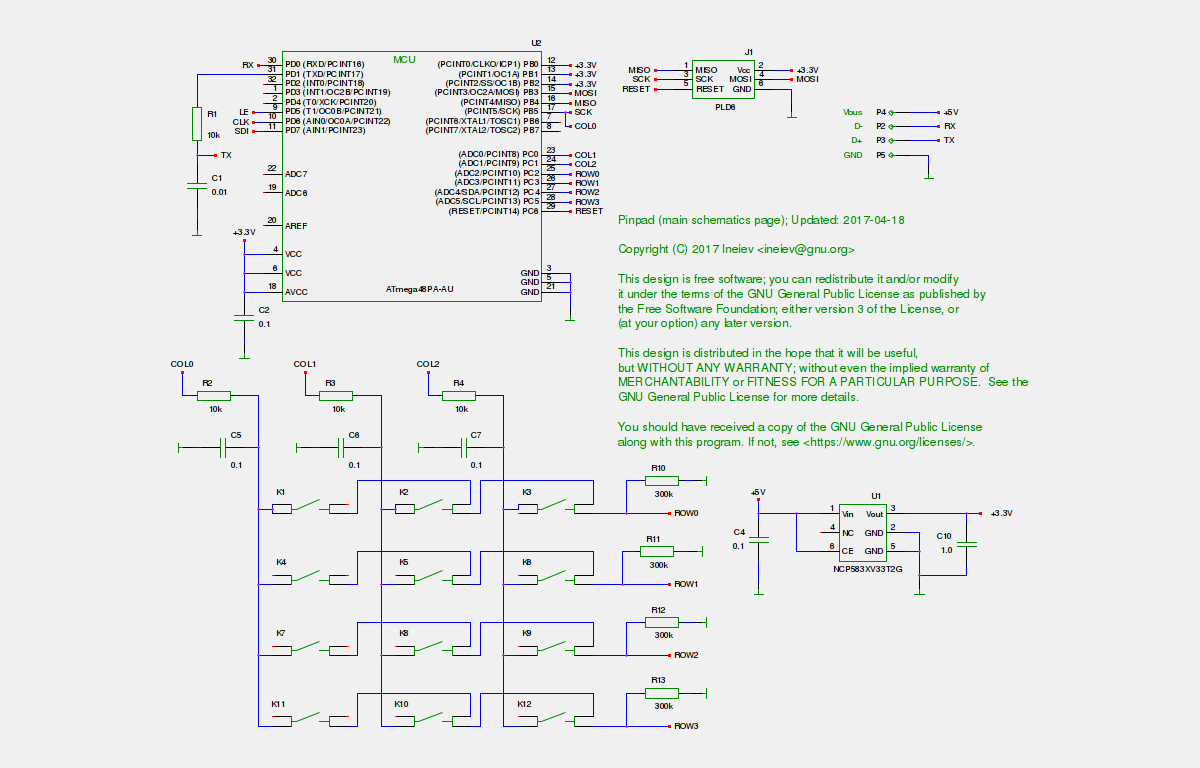
Pinpad connects to FST-01 through USART, the connection is encrypted
with Salsa20. The key is stored in EEPROM memory of pinpad and
flash memory of FST-01. Password inputs are arranged
as follows:
- FST-01 powers up ogarev.
- FST-01 generates a random 8-byte initialization vector and sends
it to ogarev, unencrypted.
- FST-01 generates a random 7-byte challenge.
- FST-01 initializes its Salsa20 sequence with the initialization
vector, uses it to encrypt a command code, the 7-byte challenge
and the secret pinpad ID, and sends the encrypted message to ogarev.
The command code contains the type of password to enter (PW1, PW3 or RC)
and the operation ("current", "new", "confirm"); command code set
also includes an empty command that just tests authentification, and
a command to update the credentials in the pinpad.
- Ogarev initializes its Salsa20 sequence with the received
initialization vector and decrypts the pinpad ID, the challenge
and the command code. If the pinpad ID doesn't match, the pinpad
decreases its try counter, when the latter reaches zero,
the credentials in the pinpad are reset to the unprogrammed state.
If the pinpad ID is correct, the command code is shown to the user
as the prompt to enter the password.
- Ogarev encrypts the command code with the challenge and sends it
back to FST-01.
- FST-01 decrypts the data and checks whether they coincide
with the data sent to ogarev. If they don't, FST-01 powers down
ogarev and cancels the operation.
- Ogarev encrypts keypresses entered by the user and sends them
to FST-01 until the input is complete.
- FST-01 powers down ogarev.
Source files
ogarev-0.6.tar.gz,
signature.
The tarball contains design files, firmware sources for the pinpad
and patches for Gnuk.
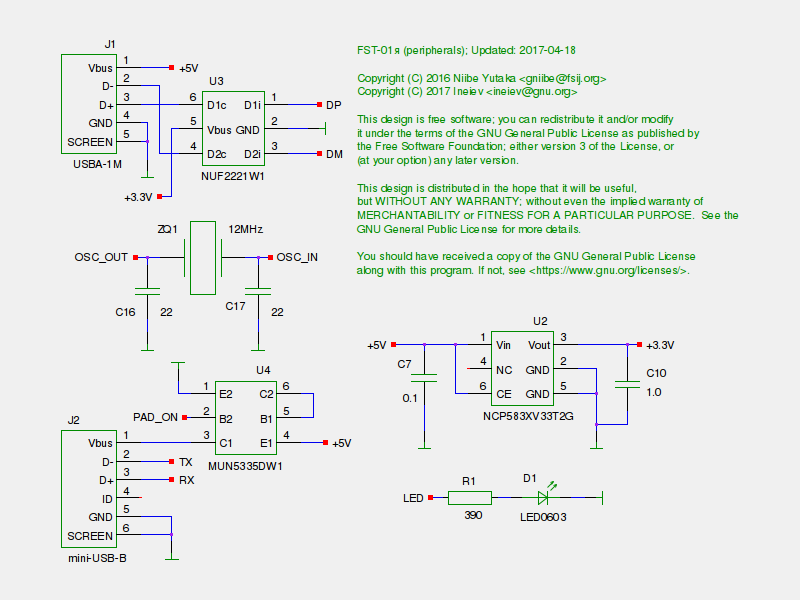
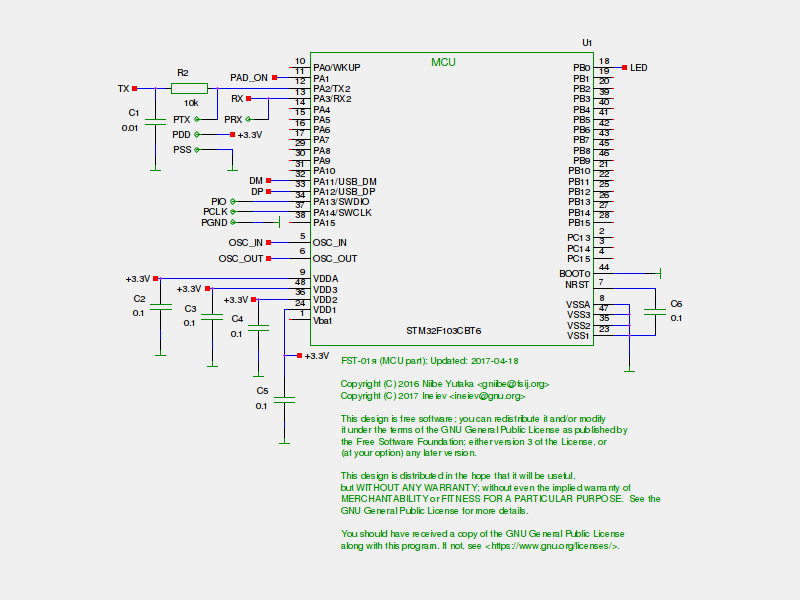
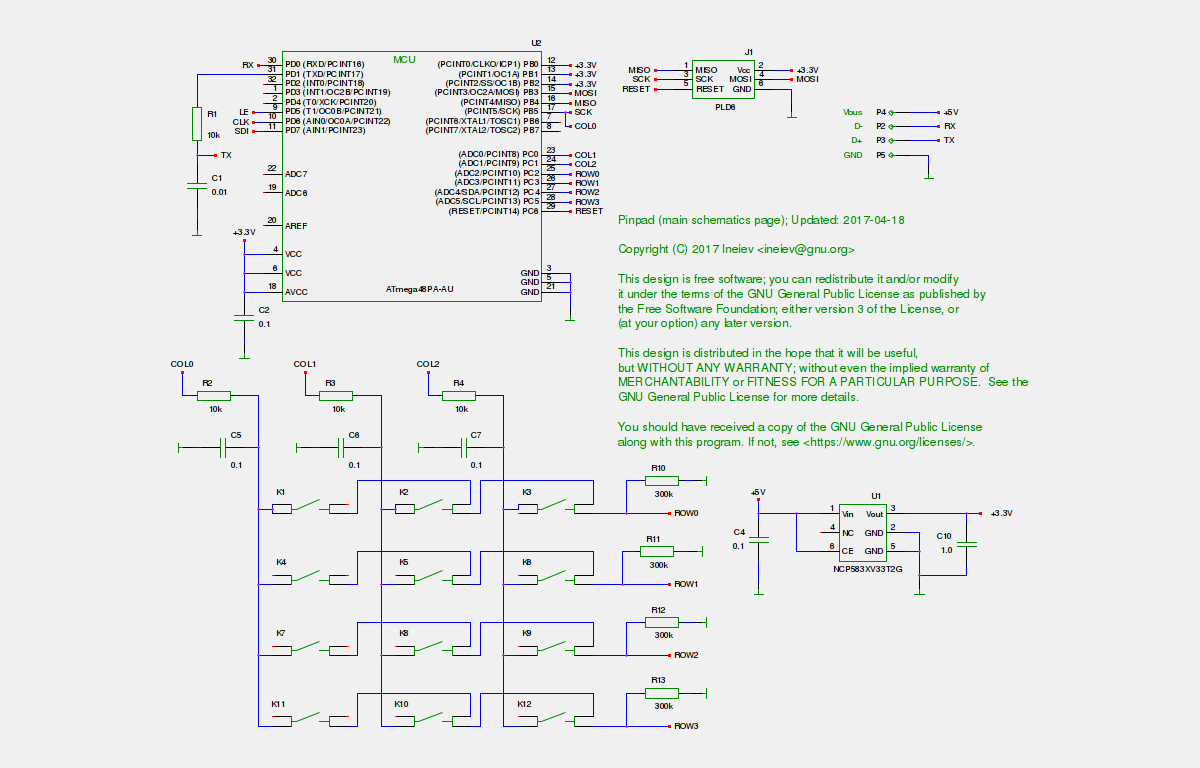
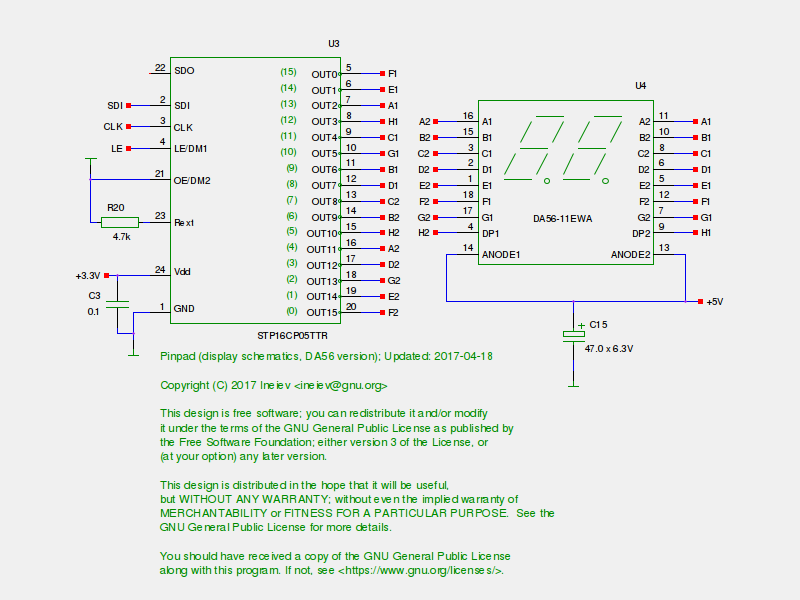
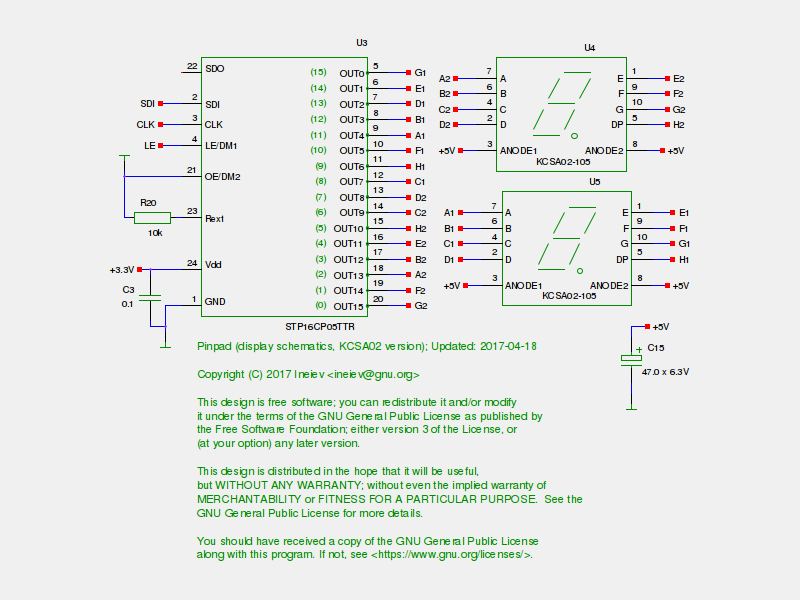
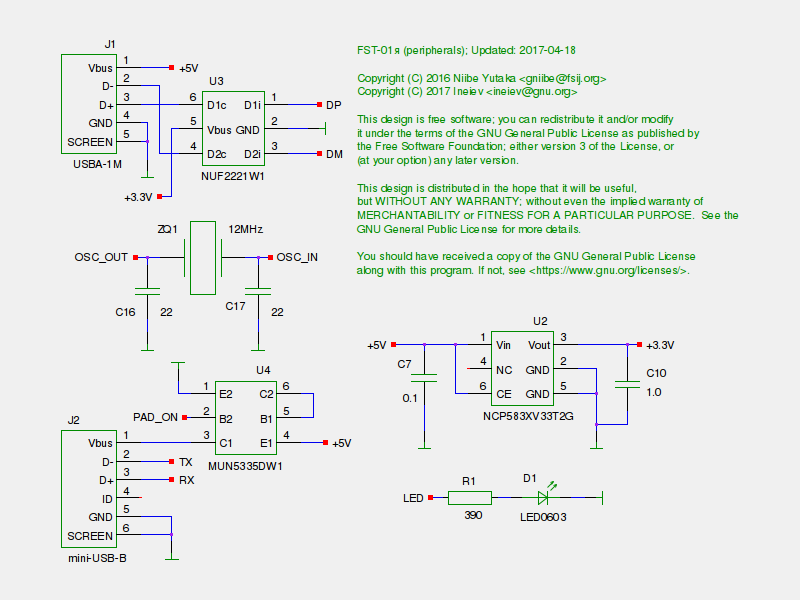
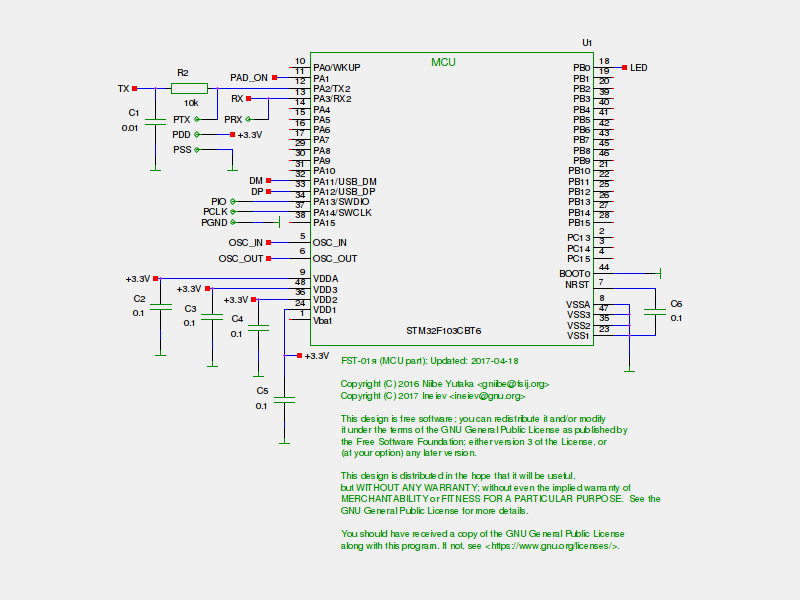
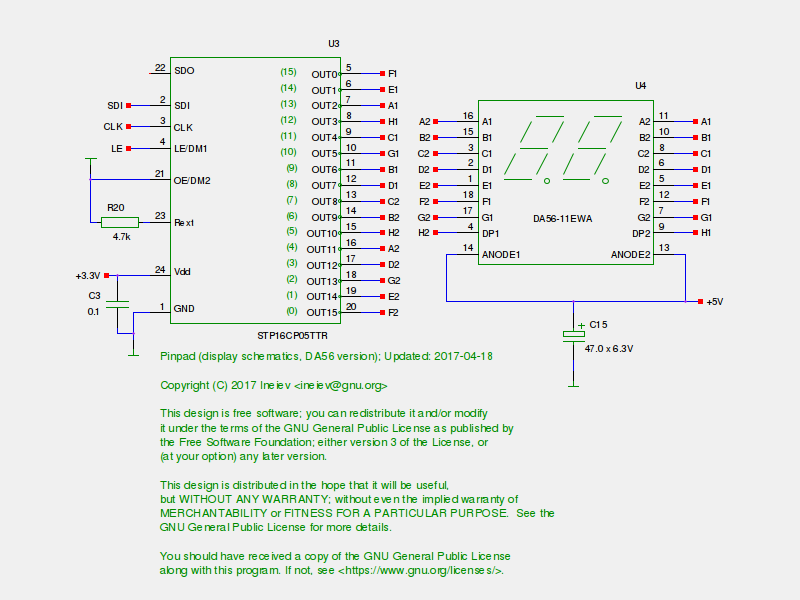
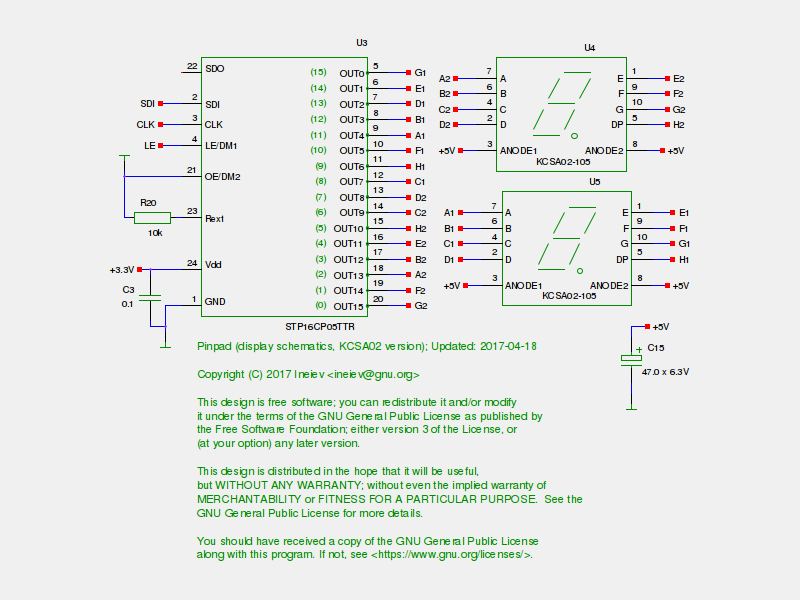
Schematics
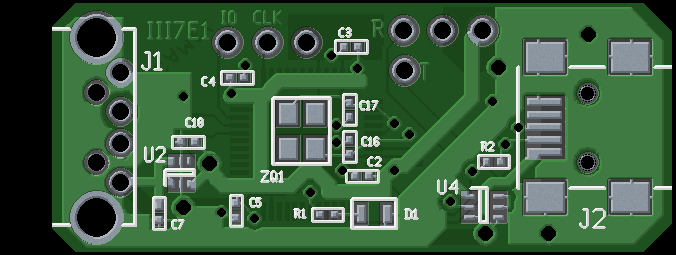
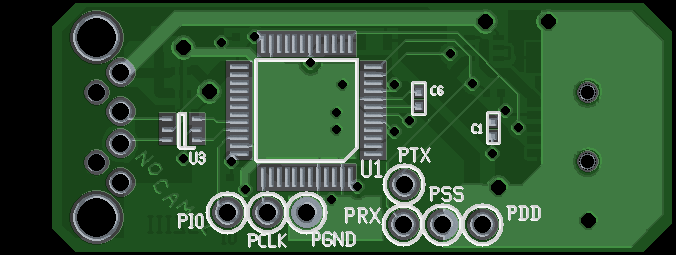
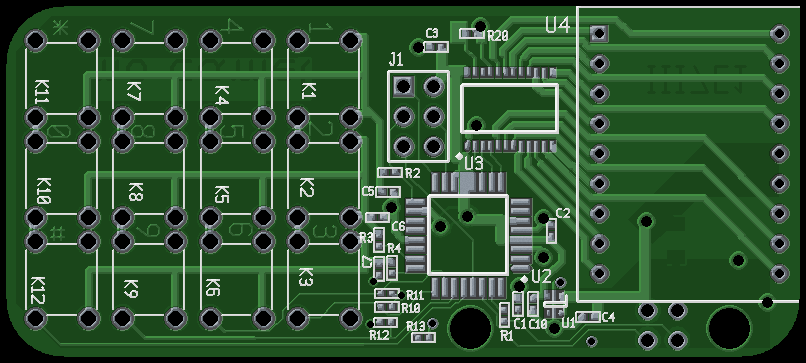
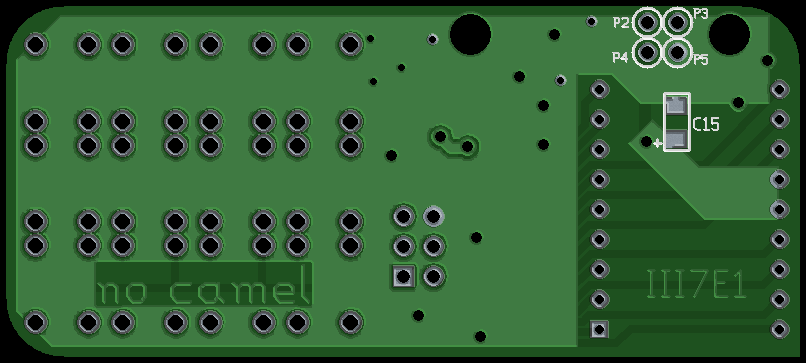
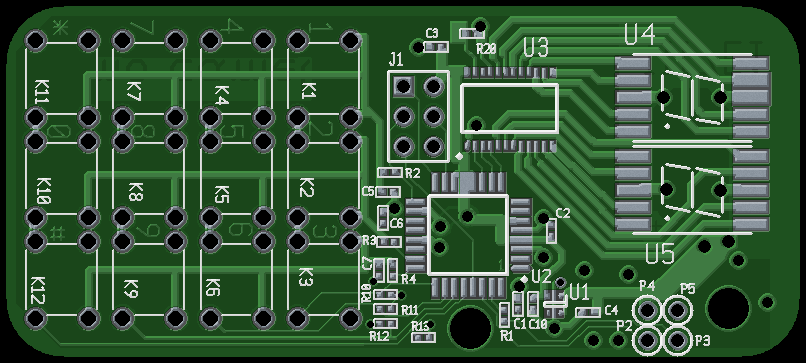
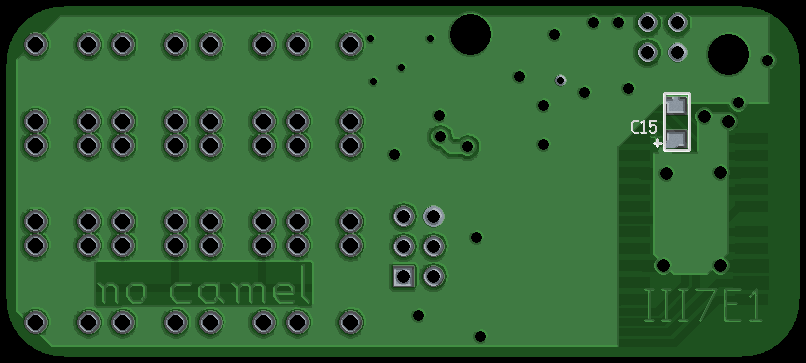
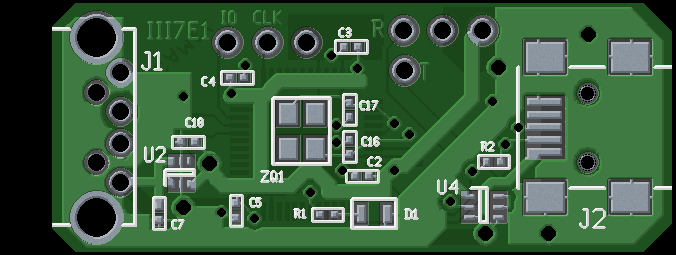
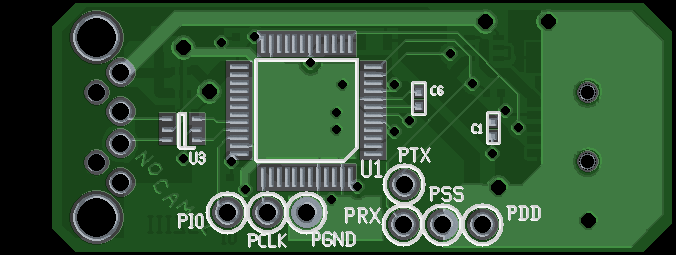
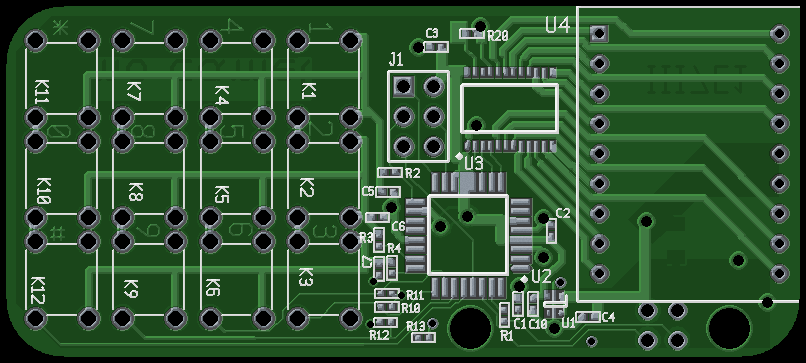
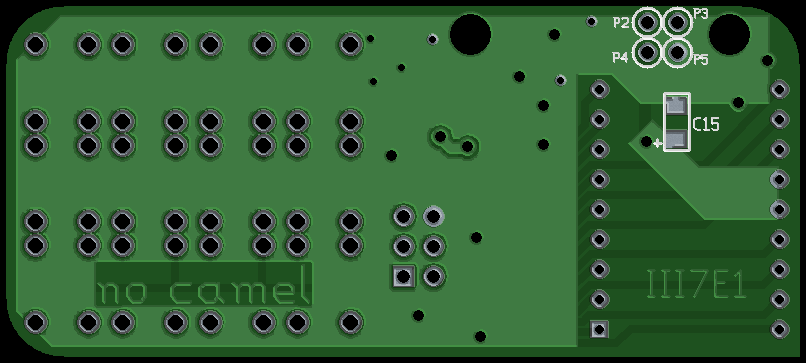
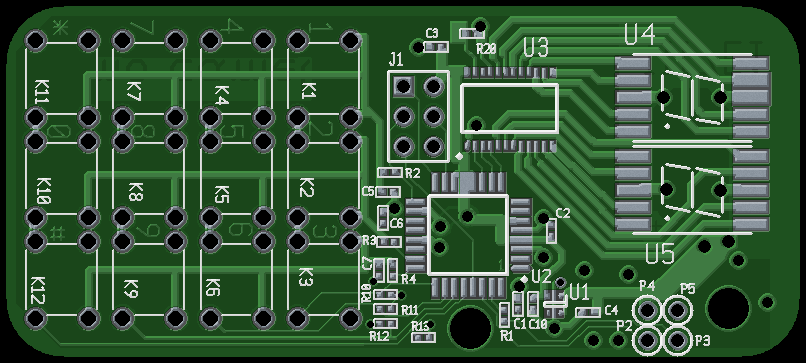
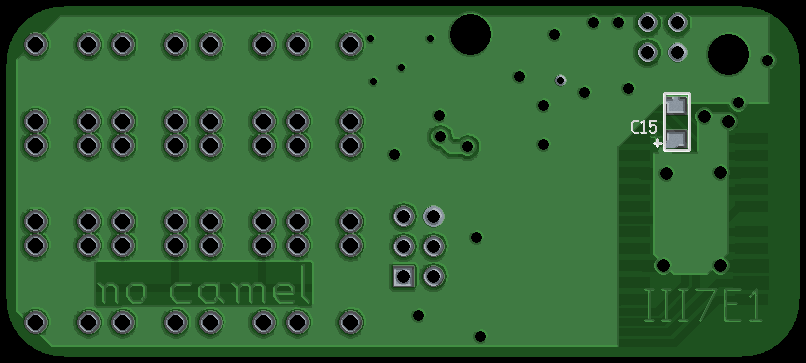
Board images
FST-01я
The pinpad is supposed to be used with a modified version of FST-01,
tough in theory the user can connect it to original FST-01 hardware.